Certfirst
444 Courses
2081 Students
 $249.00
$249.00Biometrics Systems
2 Lessons0 Students $295.00
$295.00Biometric System Performance
1 Lesson0 Students $295.00
$295.00FBI-NGI-IAFIS
1 Lesson0 Students $295.00
$295.00Biometric Standards
1 Lesson0 Students $295.00
$295.00Fingerprint Recognition
1 Lesson0 Students $295.00
$295.00Face Recognition
1 Lesson0 Students $295.00
$295.00Iris Detection
1 Lesson0 Students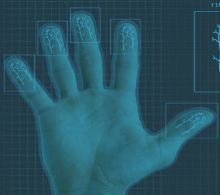 $295.00
$295.00Vein Recognition-VPR
1 Lesson0 Students
