Certfirst
CertFirst, a global integrated knowledge solution company has partnered with leading vendors to provide high quality and effective professional training solutions in the several areas of critical importance to enterprises including Project Management, Open Source, Software and Application Development, Information Security including Biometrics and others.
Biometrics and Cybersecurity
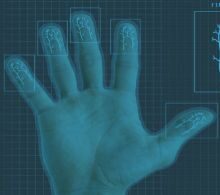
Course Description Technology simplifies many things, but security is always a problem with the advancement of technology. Cybersecurity is the protection of a computer against data theft, corruption, and loss. Biometric security is quickly becoming the preferred method of protecting businesses and individuals from hackers intent on fraud and identity theft. Fingerprint readers, iris scans, and facial recognition have become commonplace, thanks to the efforts …
$249.00Biometrics and Border Security
Course Description Fingerprints were the first biometric modality used to confirm travellers’ identities, and they are now the most extensively used modality in border control systems. Irises and faces were soon used for identification. Other biometrics are also being tested at the border by border control organisations, with many pilot projects now underway. Multimodal systems, which provide a multi-layered approach to border protection, are also …
$249.00Biometrics as a Service
Course Description Enterprises, corporations, and organisations are looking for more efficient, secure, and on-the-go business ways in today’s digital landscape. Furthermore, tech-savvy customers are driving the proliferation of portable mobile devices such as smartphones, tablets, and so on, which fuels the demand for location-independent, ubiquitous delivery platforms such as the cloud. The increasing use of biometric technology for person identification and authentication, as well as …
$295.00Speech and Voice Recognition
Course Description Speech recognition, also known as automatic speech recognition (ASR), computer speech recognition, or speech-to-text, is a feature that allows a program to convert human speech into written text. While voice recognition and speech recognition are frequently conflated, speech recognition focuses on the translation of speech from a verbal format to a text format, whereas voice recognition solely aims to recognize an individual user’s …
$295.00Signature Biometrics
Course Description A handwritten signature is a person’s name written by his or her own hand. Signature is a behavioral feature utilized in automatic user verification systems inside the biometric framework. Handwritten signatures have a long history of being used to validate a user’s identification for applications such as document authentication, credit card transactions, cheque verification, attendance recording, and forensics. Although signatures are still used …
$295.00Retina Scanning
Course Description Retina recognition is a biometric technology that uses the distinctive patterns on a person’s retina to identify them. The retina is a layer of blood vessels at the rear of the eye. The eye is placed in front of the system at a capture distance varying from 8 cm to 1 meter. The individual must line up a succession of markers as seen …
$295.00Privacy and Laws
Course Description Almost every country has implemented some form of data privacy legislation to govern how information is gathered, how data subjects are notified, and how much control a data subject has over his information once it has been shared. Failure to comply with applicable data privacy regulations may result in penalties, lawsuits, and even the prohibition of a site’s use in some places. It …
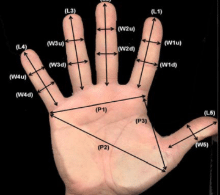
$295.00Palm Print
Course Description By increasing the security of parson’s authentication, the palmprint modality played the most important trait when compared to other biometrics traits, and it is active research that has garnered more attention for researchers interested in biometrics fields. The little part of the palm surface that contains more information that is useful for person identification systems; also, it has a unique characteristic (uniqueness meaning …
$295.00Multi modal Systems
Course Description All of the biometric systems we’ve explored thus far have been unimodal, relying on a single source of information for authentication. Multimodal biometric systems, as the name implies, accept information from two or more biometric inputs. Unimodal systems must cope with a variety of issues, such a lack of confidentiality, non-universality of samples, the extent of the user’s comfort and freedom while interacting …
$249.00Keystroke Dynamics
Biometrics factors provide IT decision-makers with an enticing prospect: an authentication factor that hackers cannot steal or replicate. Threat actors regularly crack passwords or guess them based on social media data. SMS communications can be intercepted by skilled hackers, and some can even send bogus SMS messages as part of a unique phishing attempt. Threat actors can reproduce the signature of hard tokens with time …
$295.00Gait Recognition
Course Description One of the biometric identification technologies that has received a lot of interest is gait recognition. There have been numerous theories arguing that a person’s walking style is a distinct behavioral trait that may be used as a biometric. In contrast to other biometric identification technologies such as face recognition, gait recognition is widely recognized as the most essential noncontactable, noninvasive biometric identification …
$295.00DNA Recognition
Course Description There are a few reasons why DNA is one of the most widely used biometric technologies in the world. The first reason is that many people feel that DNA is the most exact and never fails technology. Of course, there is no such thing as 100% accuracy because something can go wrong at any time and mistakes occur. However, when this occurs, it …
$295.00Hand Geometry Recording
Course Description Hand geometry recognition is the most extensively used biometric type. Systems are widely used due to their ease of use, public acceptance, and integration capabilities. One of the hand geometry characteristic’s drawbacks is that it is not highly unique, restricting the hand geometry system’s uses to verification jobs exclusively. For time and attendance purposes, many businesses use hand geometry systems in conjunction with …
$295.00Vein Recognition-VPR
Course Description Vein pattern recognition (VPR), one of the most promising biometric technologies, is swiftly taking root around the world and may eventually dominate applications where human focus is critical. Among the reasons for VPR’s increasing acceptance and use are the following: it is more accurate than many other biometric methods, it is more resistant to spoofing, it focuses on people and their privacy, and …
$295.00